How I Fingerprint My Own API to Catch Scrapers
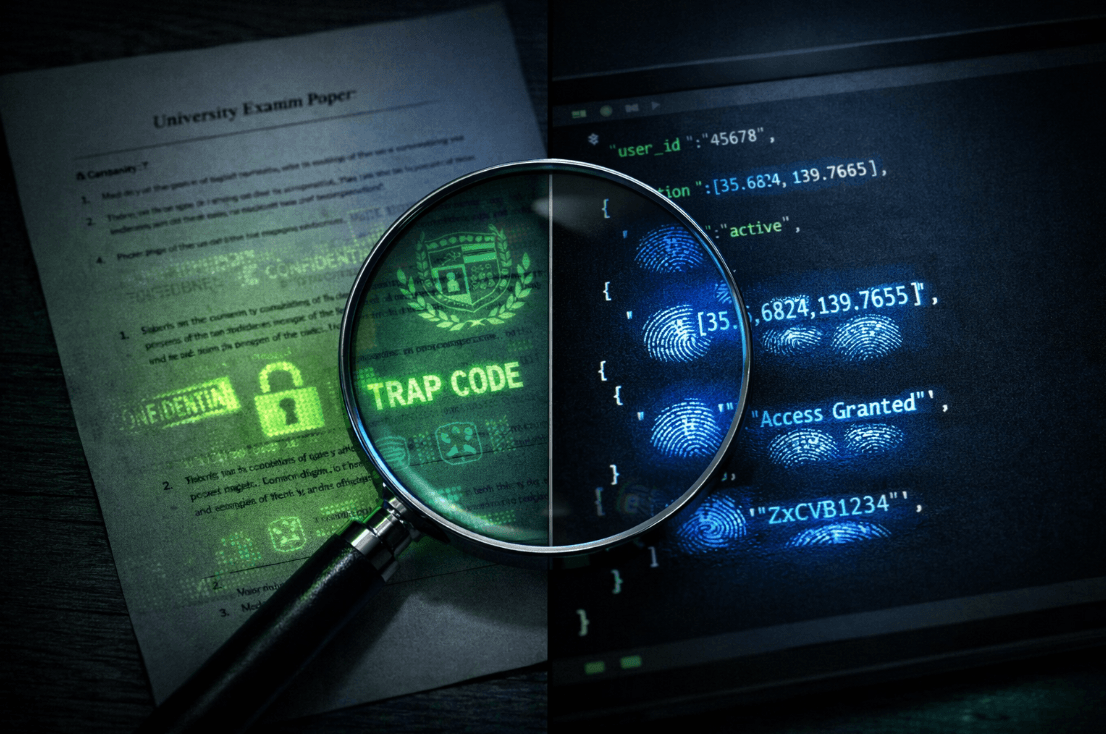
Trap streets, phantom records, and the watermarking tricks that catch scrapers
Search for a command to run...
Series
A raw, technical build in public series documenting how I'm building Tripvento from zero — a B2B travel API that ranks hotels using geospatial intelligence and semantic AI. No fluff, no vanity metrics. Just real decisions, real code, and real tradeoffs from a solo engineer shipping fast.
Trap streets, phantom records, and the watermarking tricks that catch scrapers
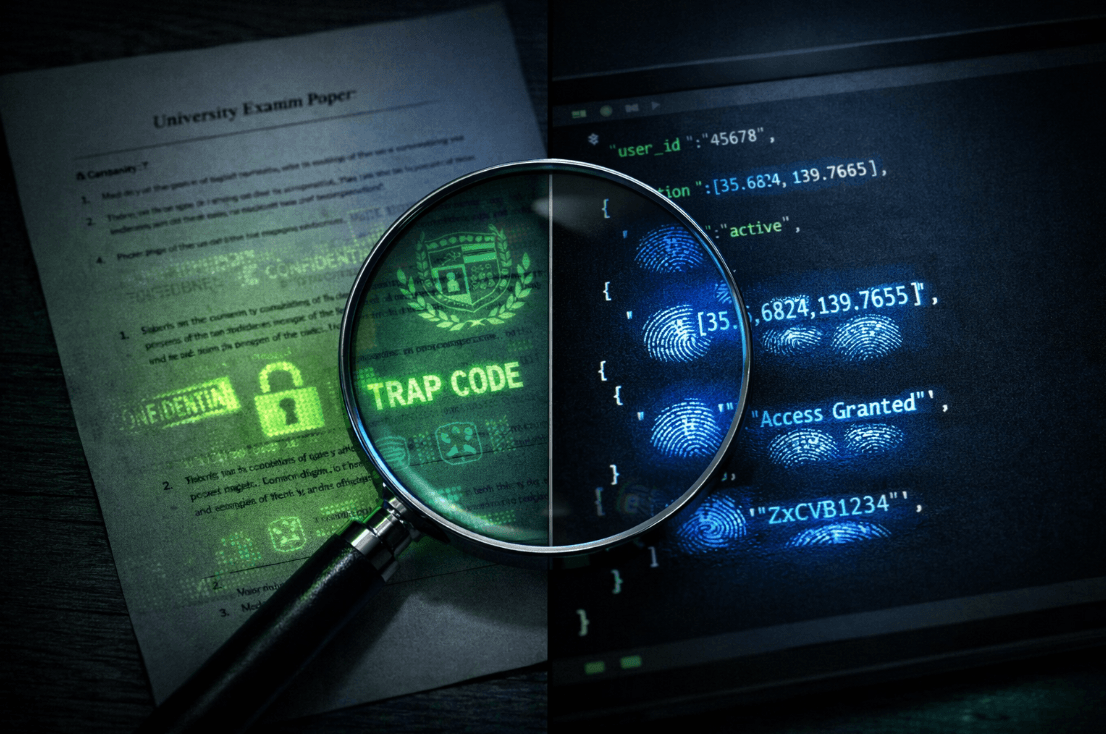
Why transformed data still reveals where it came from

How a practical joke turned into an LLM honeypot, two free security tools, and a canary endpoint that fingerprints AI scrapers.
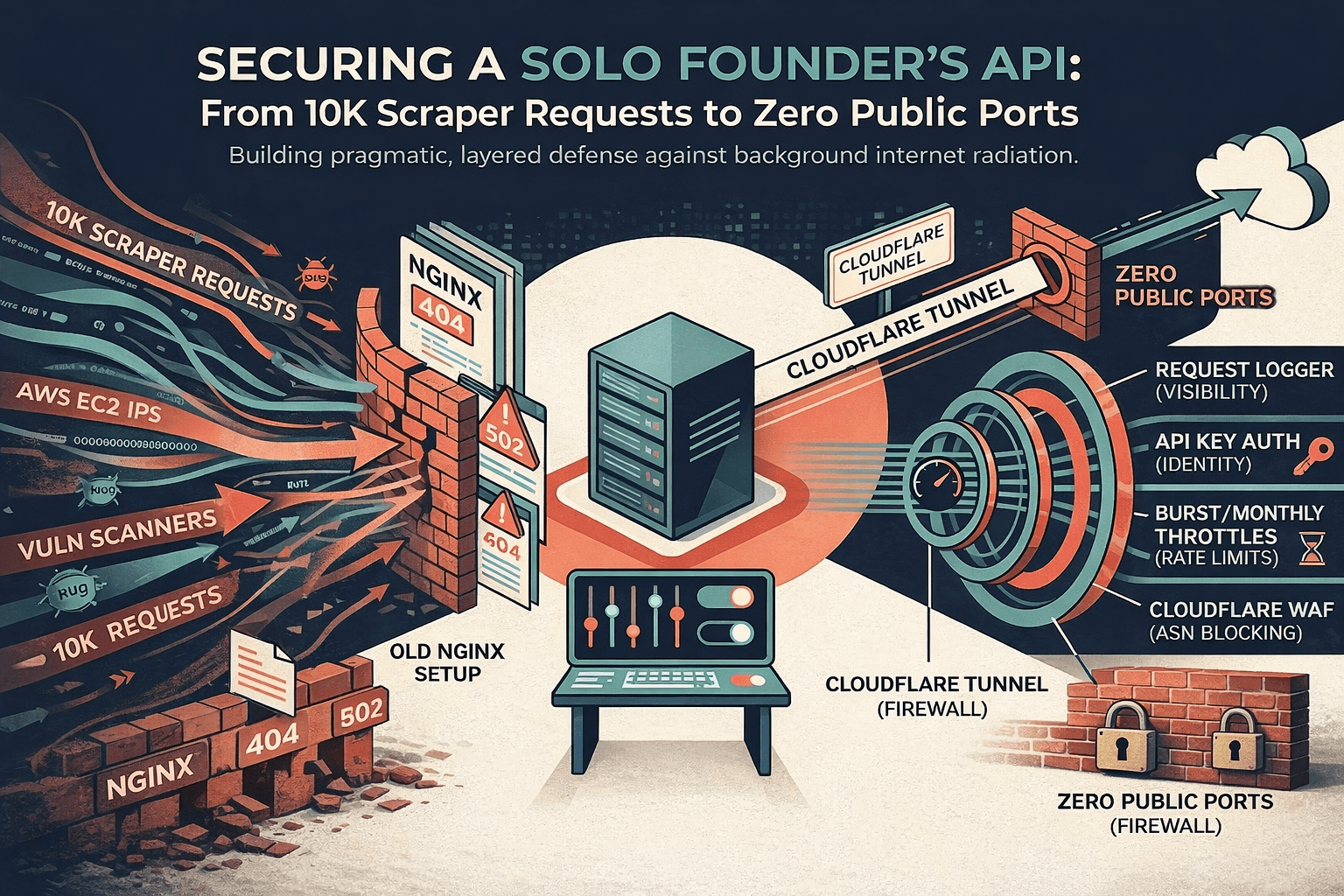
I built security for "no one's looking." The open web is "everyone's looking." This is the post mortem of closing that gap. The thesis: identity + perimeter shift + observability beats reactive blocking.
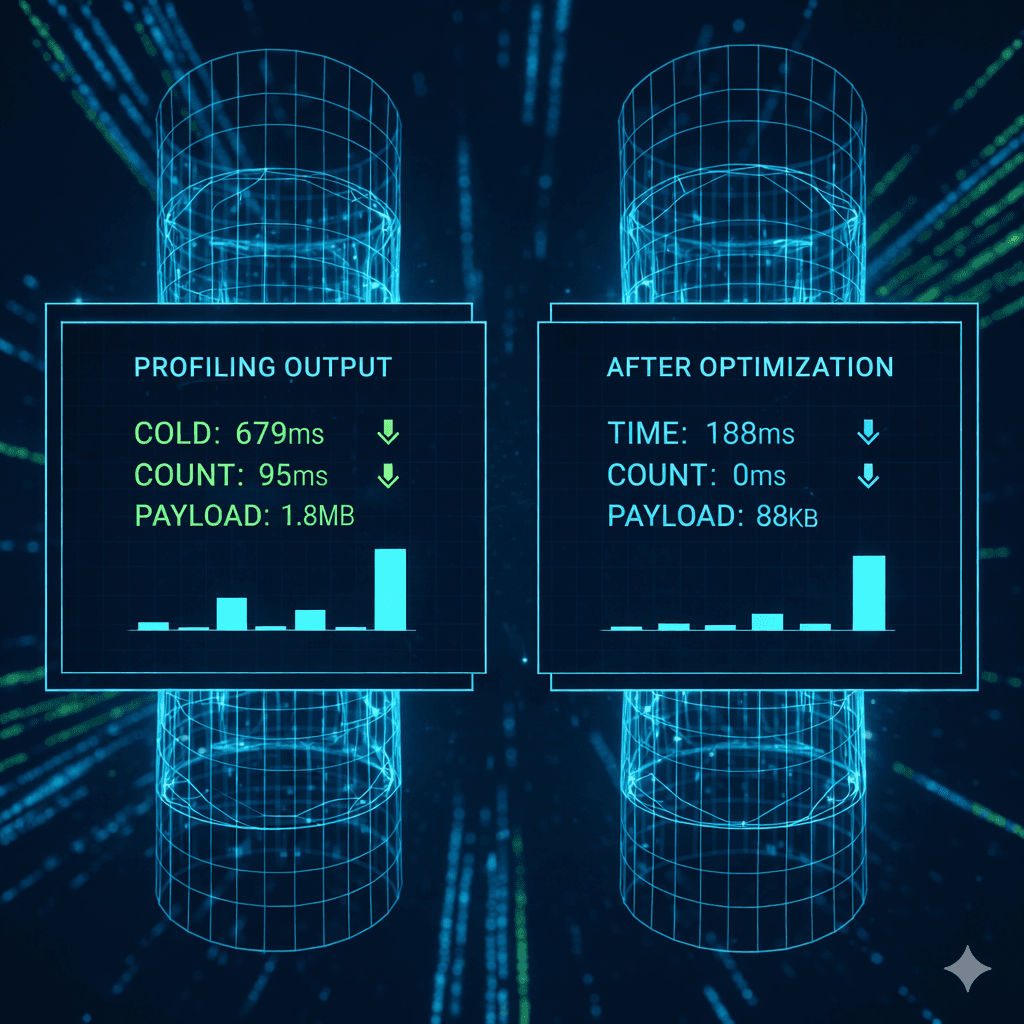
When my API slowed down, I didn’t add Redis. I didn’t upgrade the droplet. I opened a Django shell and started measuring.
Cheapest checks first: A 64 cent, multi model pipeline that audits itself.